Microsoft Identity and Access Management - Overview
Executive Summary
As organizations grow, they tend to accumulate multiple systems and standards for storing, managing, and using digital identities. These systems can include directory services, human resource (HR) databases, financial systems, and custom applications, as well as Web sites for employees, customers, and partners.
The complexities that result from having multiple identity systems and standards generate higher costs, increased management overhead, and more numerous security vulnerabilities that grow as application surface area increases. The Microsoft Identity and Access Management Series helps organizations take control of their environments and reduce complexity. The series does this by explaining the concepts, approaches, technologies, and solutions available for solving identity and access management problems.
Note Identity and access management combines processes, technologies, and policies to manage digital identities and specify how they are used to access resources.
The series shows how to achieve solid business results using Microsoft technologies in heterogeneous IT environments while concentrating on the key issues of total cost of ownership (TCO), security, and the growing need for information access beyond organizational boundaries. The series provides solutions that balance the need for short-term business results with a long-term security and management strategy.
Each paper incorporates field experience that deals with real-world problems, and the solutions offered are technically validated. Where appropriate, the papers in the series provide technical guidance on implementing, testing, and operating each scenario-based solution that they address. Microsoft engineering teams, architects, consultants, support engineers, partners, and customers contributed to, reviewed, and approved each paper.
Microsoft worked with PricewaterhouseCoopers to develop the Microsoft Identity and Access Management Solution, which was the precursor to this series. This combination of Microsoft technology and product expertise with PricewaterhouseCoopers' industry expertise provides you with the best possible tools to plan and design effective identity and access management solutions for your organization.
The following figure illustrates the content and logical divisions within the Identity and Access Management Series v 1.4.

Figure 1. The Identity and Access Management Series Papers
Questions and Answers
This section provides answers to the most common questions received from the feedback alias. Please direct questions and comments about this guide to secwish@microsoft.com.
My organization does not run Active Directory® or any Microsoft® Windows® products. What's in this guide for me?
Although the Microsoft Identity and Access Management series uses a scenario based on Windows Server® 2003, Active Directory, and MIIS 2003 SP1, the principles that this guide highlights apply to many different solutions. Because of the large range of identity stores that this product supports, many organizations with no other Microsoft products have implemented MIIS 2003 If you have a large, distributed enterprise with multiple identity stores, you may find that MIIS 2003 can provide you with the integration facilities you need, without Active Directory or any other Microsoft products.
We are only a small company – why should I be concerned about identity and access management?
Even small companies may need to run multiple identity-aware applications that require staff to log on repeatedly. Awareness of identity and access management principles will help you avoid poor design decisions that require complex identity management solutions.
I'm the CIO of a large national company, and I need to be able to sell the business benefits of identity management to the senior executives. However, they're not technical, and I don't want to blind them with jargon. Where can I find information that will help me build a convincing financial case?
The Fundamental Concepts paper lists the significant benefits and cost savings that identity management can bring, and does not cloud the picture with technology.
My Directory Services team spends a lot of time simply ensuring that our e-mail systems and directory services are kept in synchronization with our telephone and HR database. How can we plan and implement a system to reduce this workload?
The Identity Aggregation and Synchronization paper in this series discusses the principles behind linking multiple identity stores, and then takes you through the steps to set up this type of integration.
We have multiple directory services, and our helpdesk personnel constantly have to deal with users forgetting their passwords. What can we do to minimize the time spent on this activity?
The Password Management paper takes you through the process of implementing self-service password resets, and then propagating these new passwords to multiple identity stores. This paper also shows you how to use the Windows Security dialog box to change multiple passwords in one operation.
The company I work for has a large turnover of contractors, and it currently takes us far too long to set up new user and e-mail accounts. We are also aware that we are not disabling user accounts quickly enough when people leave. How could we implement this sort of functionality?
The Tools and Templates for the Provisioning and Workflow paper includes a sample workflow application that integrates with MIIS 2003 to provide advanced provisioning and approval functions. You can automate the process of provisioning user accounts, and route messages to managers to remind them that their approval is required.
I don't use Sun Solaris, but I do need to integrate large numbers of Red Hat Linux workstations into Active Directory. Which paper do I need to read?
The step-by-step procedures in Chapter 5 of the Intranet Access Management paper only require minimal customization to work with the Red Hat Linux distribution.
We need to identify and authenticate members of the public who use our subscription-based services. Is there any information in this series that can help us?
The Extranet Access Management paper explains how to use Microsoft Passport authentication to provide self-service authentication of large numbers of external users.
We have a custom identity-aware application that we want to migrate from Linux to the .NET Framework. What design decisions should we make to ensure the migrated application can manage identities effectively, and what development platform should we choose?
The paper Developing Identity-Aware ASP.NET Applications shows you how to implement identity awareness into applications that use the .NET Framework. .NET Framework applications can be built using the Visual Studio® .NET development environment in Visual Basic®, Visual C++®, or Visual C#®.
Audience and Structure
The Microsoft Identity and Access Management Series targets security specialists, architects, technology decision makers, IT professionals, developers, and consultants responsible for planning, designing, and implementing solutions for identity and access management. Other participants in identity and access management projects may also find these papers and resources useful.
The series divides into three parts, with each part containing one or more papers. The parts in the series are as follows:
Part I — The Foundation for Identity and Access Management is intended for people without a background in identity and access management, and those who want to improve their understanding of Microsoft identity and access management products. This part familiarizes readers with the underlying concepts that the remaining papers discuss in more detail.
Part II — Identity Life-Cycle Management is intended for architects, IT professionals, and administrators responsible for managing numerous identities, although it contains information of interest to decision makers as well.
Part III — Access Management and Single Sign On is intended for architects, IT professionals, and developers who are responsible for integrating applications and platforms with enterprise directory and security services while increasing access to a growing number of customers and partners. Each of these papers also begins with information of interest to decision makers.
The Part II and Part III papers in this series all follow a similar structure to meet the needs of several audiences. The first section of the paper describes a topic generically and the remaining chapters provide one or more detailed solution scenarios with implementation guidance and usable samples called Tools and Templates. The chapter structure of these papers is as follows:
- Introduction. Summarizes the paper and the contents of each chapter.
- Approaches. Describes the many approaches and technologies available to solve the problems that the paper covers.
- Issues and Requirements. Examines the issues confronting Contoso Pharmaceuticals (a fictitious organization representative of many organizations) and how these issues drive their solution requirements.
- Designing the Solution. Presents the solution that Contoso implemented, together with the prerequisites, the logical design, and the network layout.
- Implementing the Solution. Provides guidance on how to implement the Contoso solution design that addresses the issues identified earlier.
- Testing the Solution. Describes a series of activities that you can perform to validate that the solution implemented in the previous chapter works as intended.
- Operational Considerations. Introduces a few additional operational activities that should be considered for specific solution scenarios, but does not provide comprehensive operational guidance.
Part I — The Foundation for Identity and Access Management
The first part of the series provides the foundation for understanding identity and access management and provides background materials for the papers in Parts II and III.
Fundamental Concepts
This paper introduces the business and IT challenges that relate directly to identity and access management and then outlines the approaches and technologies available to overcome them. The paper discusses key concepts and terminology that apply to identity and access management such as authentication, authorization, trust, federation, security auditing, provisioning, and directory services.
The paper reviews a range of technologies that organizations can use to build identity and access management solutions. These technologies include:
- Microsoft® Active Directory® directory service
- Microsoft Active Directory Application Mode (ADAM)
- Microsoft Identity Integration Server 2003 with Service Pack 1 (MIIS 2003 SP1)
- Microsoft Passport
- Microsoft Internet Information Services (IIS)
- Microsoft Windows® Authorization Manager
- Microsoft Windows Credential Manager
- Kerberos version 5 authentication protocol
- Public key infrastructure (PKI) and x.509 certificates
- Secure Sockets Layer (SSL)
- Transport Layer Security (TLS)
- Lightweight Directory Access Protocol (LDAP)
Platform and Infrastructure
This paper introduces the fictitious company Contoso Pharmaceuticals to describe the business, technology, and security challenges that a typical organization faces related to identity and access management. The Contoso Pharmaceuticals scenario continues by describing an enterprise technology infrastructure based on the Microsoft Identity and Access Management Platform and that helps address these challenges. This platform is the foundation for all of the solutions described in the other papers.
Part II — Identity Life-Cycle Management
Part II focuses on the management of users, credentials, and entitlements — keeping them current, synchronized, and consistent with governing policies.
Identity Aggregation and Synchronization
Maintaining multiple directories and identity stores is a significant source of management cost and complexity. Years of product acquisitions, internal development, and platform implementations tend to create heterogeneous systems of considerable complexity.
Migrating to a single directory and security model is unlikely to be an achievable short or even medium-term goal for many organizations because of the cost, timeframe, and complexity involved in such an undertaking. However, it is possible to aggregate and synchronize all the directories within an organization to enable centralized management and administration while reducing costs.
This paper discusses the many approaches and technologies available for identity synchronization and then describes how to aggregate and synchronize multiple directories and identity stores across a heterogeneous environment that includes Active Directory, Microsoft Exchange, Lotus Notes, and Sun ONE Directory Server 5.1 (formerly iPlanet Directory Server) using MIIS 2003 SP1.
Password Management
Poor password management can have a dramatic impact on the security and financial health of any organization. Unfortunately, attacks designed to steal or capitalize on weak passwords occur frequently today. In many cases, these attacks can establish a presence to launch even more sophisticated and dangerous intrusions on corporate networks.
In addition to addressing these concerns, aggregating the processes required to manage and enforce a strong password policy for your organization offers many other benefits. Effective password management enables your organization to reduce overhead associated with password changes and resets, simplifies the user experience to update passwords, improves overall security, and helps your organization to comply with many government regulations specific to password security controls.
The "Password Management" paper outlines different approaches to password management, and addresses the technical issues that effective password management involves. The paper uses a fictitious organization to illustrate the process of how to determine password policy requirements, carry out sequential procedures to enforce a strong password policy, and then manage the organization's passwords through both an intranet and an extranet. Finally, the paper discusses how to validate the password management implementation and perform common operational and maintenance tasks.
Provisioning and Workflow
Large organizations today often have complex and poorly designed processes for provisioning user identities across multiple systems. For example, in some organizations, it can take up to two weeks before new information workers can access e-mail and the applications that they need for their jobs. The manual, task-intensive processes that are typically involved in identity provisioning add overhead, delay employee productivity, and often lead to a network environment that is not secure.
The "Provisioning and Workflow" paper discusses how to provision identities automatically into multiple directories in a heterogeneous environment. The paper also discusses how to manage security and e-mail group memberships, and describes a workflow process that can extend automated processes.
The Overview and Planning materials (chapters 1 through 3) help architects and IT implementers to understand the business challenges, approaches to, and benefits of user provisioning, group management and integrated workflow. The Implementation sections (chapters 4 through 7) provide a concise set of detailed instructions for designing, implementing, and managing HR-system driven user provisioning, self-service user provisioning, and group management. An example of an integration process could be to use a SAP-based HR database as the primary source of identity information. The Provisioning and Workflow paper provides practical illustration of this integration.
Part III — Access Management and Single Sign On
Part III focuses on the processes and technologies for controlling access to resources. Access management covers topics such as authentication, single sign on (SSO), credential mapping, authorization, trust, and security auditing.
Intranet Access Management
Organizations often have to contend with operating systems, applications, and directory services from different vendors. The challenge is to either integrate each operating system and application into your organization's preferred directory and security services, or provide approaches for an alternative SSO experience such as credential mapping.
The Microsoft Windows operating system supports several standards that enable many other operating systems and third-party applications to achieve cross-platform integration. Integrating third-party products with Windows-based security and directory services can lower management costs, reduce complexity, improve security administration, and provide a better user access experience.
This paper describes several approaches for integrating applications and platforms with Microsoft directory and security services. These approaches range from tight directory integration using protocols such as the Kerberos version 5 authentication protocol and LDAP to credential mapping techniques using SharePoint® Portal Server 2003, BizTalk® Server 2004, or Host Integration Server 2004.
This paper defines the most common techniques for achieving intranet SSO, providing access management, and enabling platform and application integration. The paper also provides implementation guidance for the following solution scenarios:
- Integrating UNIX workstations with Active Directory
- Integrating SAP R/3 Application Server authentication using the Kerberos version 5 authentication protocol
Extranet Access Management
Providing customers, partners, and employees with access to Web applications and online services is an increasingly important business driver in many organizations. IT departments need to provide a seamless, secure sign on experience for such applications and services while keeping directory provisioning and maintenance costs low.
This paper describes the approaches for managing secure Web access for business-to-customer (B2C), business-to-employee (B2E), and business-to-business (B2B) extranets. The paper also includes implementation guidance for the following solution scenarios:
- B2E extranet Web access and SSO using X.509 certificates
- B2C extranet Web access and SSO using Microsoft Passport
Developing Identity-Aware ASP.NET Applications
Most organizations accumulate legacy applications that do not integrate well with each other or with enterprise directory services. The challenge for these organizations is to create an architectural model that better integrates their internally developed applications with their identity and access management infrastructure.
This paper describes approaches for building Active Directory–integrated multi-tier Microsoft ASP.NET applications (for authentication, authorization, and security logging) plus detailed implementation guidance and ASP.NET code samples (in Microsoft Visual C#® and Visual Basic® .NET) for:
- Intranet Web applications that use Windows-integrated authentication and Windows Authorization Manager.
- Extranet Web applications for B2B, B2C, and B2E scenarios using Windows authentication (including Forms-based authentication, X.509 certificates, and Microsoft Passport) and Windows Authorization Manager.
Download the Series
The following resources are included with the Microsoft Identity and Access Management Series download:
- A list of files contained in the download package.
- Release notes containing revision information, resolutions to known issues, and other critical information for the readers. The series will be updated on a regular basis; check this page periodically to determine if any updates have occurred since your last visit.
Navigating the Papers
The following figure shows how the papers within the series interconnect.

Figure 2. Navigating the Identity and Access Management Series
Accessing the Series Tools and Templates
The Identity and Access Management download package includes the Tools and Templates installation file, Identity and Access Management Tools and Templates.msi. The Tools and Templates that are part of this download include text-based scripts, code samples, and configuration files related to identity and access management, but do not include any executable programs or compiled code.
Note These samples are provided as examples only. Be sure to review, customize, and test these tools and templates before you use them in a production environment.
When you run the installer file, the resulting folder structure (depending on where you install it) will look similar to the one shown in the following figure.
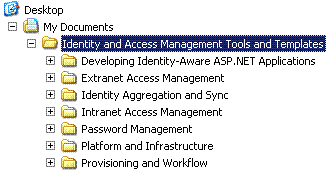
Figure 3. The Tools and Templates folder structure
This guide assumes that you have installed the Tools and Templates into the default location, %UserProfile%\My Documents\Identity and Access Management Tools and Templates. If you use a different installation location, ensure that you use the correct path in all of the steps in this document.
Note In exceptional circumstances, the Tools and Templates MSI package can produce an error during the installation process. See the Identity and Access Management Series Readme.htm file for more information.
Understanding the Style Conventions in this Series
The following table lists the style conventions that are used in the Microsoft Identity and Access Management Series.
Table 1. Style Conventions
| Element | Meaning |
| Bold | File names, user interface elements and output text appear in bold. |
| Italic- or -<Italic> | Italic is applied to characters that the user types and they may choose to change. Italic characters that appear within angled brackets represent variable placeholders where the user must supply specific values. Example: <Filename.ext> indicates that you should replace the italicized filename.ext with another filename that is appropriate for your configuration. Italic is also used to represent new terms. Example: Digital identity — The unique identifier and descriptive attributes of a person, group, device, or service. |
| Monospace code or command font | This font is used to define code samples. Example: public override void Install(IDictionary savedState) This font is also used to define commands, switches, and attributes the user types at a command prompt. Example: At the command prompt, type the following: CScript SetUrlAuth.vbs |
| %SystemRoot% | The folder in which the Windows operating system is installed. |
| Note | Alerts the reader to supplementary information. |
| Important | Alerts the reader to supplementary information that is essential to complete a task. |
| Caution | Alerts the reader that failure to take or avoid a specific action could result in the loss of data. |
| Warning | Alerts the reader that failure to take or avoid a specific action could result in physical harm to the user or hardware. |
Feedback
Please direct questions and comments about this guide to secwish@microsoft.com.
Complementary Solutions from Microsoft
Microsoft offers the following solutions that complement the content in the Identity and Access Management Series.
Microsoft Solutions for Security and Compliance
This series is produced by the Microsoft Solutions for Security and Compliance (MSSC) team, which has also produced the following security guidance:
- Windows Server 2003 Security Guide
- Windows XP Security Guide
The Microsoft Identity and Access Management Series was prepared and tested on computers configured using these security guides.
Windows Server System Reference Architecture
Windows Server Systems Reference Architecture (WSSRA) provides lab-tested and proven architectural blueprints and implementation guidance. The Microsoft Identity and Access Management Series was prepared and tested on Windows Server System Reference Architecture.
Microsoft Solutions for UNIX Migration
The Solution Guide for Windows Security and Directory Services for UNIX Download enables Microsoft Windows Server™ 2003 Active Directory, Kerberos, and LDAP services to be used for authentication and authorization within heterogeneous Microsoft Windows and UNIX environments.
Consulting Services
There are many consulting services that are available to assist organizations with their identity and access management initiatives. This section lists some of the systems integrators specializing in identity and access management.
Note A complete list of partners that are certified in Microsoft technologies is available from the Microsoft Resource Directory.
Microsoft Services
Microsoft Services exists to ensure that Microsoft technology delivers the performance and return on investment (ROI) that you expect while helping to minimize the inherent risks in complex implementations. Microsoft Services offers a range of packaged consulting services that are based on years of experience implementing Microsoft solutions.
Using best-practice models from Microsoft, Microsoft Services offers frameworks for solution development and ongoing operations. These frameworks are used by Microsoft product development and IT groups. Used with our innovative technology centers, Microsoft Services helps reduce your risks and time to market by prototyping and evaluating your solutions prior to deployment in your IT environment. Using these centers, Microsoft Services and its partners can often prototype solutions in weeks, not months.
Microsoft consultants have considerable experience in implementing identity and access management solutions for large organizations and have industry-leading experience with all the Microsoft technologies that this series covers.
Accenture
Committed to delivering innovation, Accenture collaborates with its clients to help them achieve high performance. With deep industry and business process expertise, broad global resources, and a proven track record, Accenture can mobilize the right people, skills, and technologies to help clients improve their performance.
Enterprise integration—which uses technologies and standards to connect and streamline business processes—is one of the key challenges facing clients today. Accenture's collaborative approach first identifies the right set of tools and technologies and then implements the integration solutions that will help drive business performance. Web services technology has a critical role to play in this area.
Avanade
Avanade is the premier global technology integrator for Microsoft enterprise solutions. Avanade creates value for its customers by using Microsoft enterprise technology to design, build, and deploy customized, reliable architectures and scalable infrastructures to increase profitability, improve speed-to-market, and accelerate growth. Avanade is focused on helping Global 2000 customers optimize existing and future Microsoft investments within their heterogeneous IT environment.
Cap Gemini
Cap Gemini Group is one of the largest management and IT consulting organizations in the world. The company offers management and IT consulting services, systems integration, and technology development, design, and outsourcing capabilities on a global scale to help businesses continue to implement growth strategies and leverage technology.
Cap Gemini Ernst & Young is on the forefront of providing global security services through Adaptive Security, the market-leading approach to dealing with information security. Adaptive Security places Identity & Privilege Management technology as a core component of an integrated security infrastructure. This unique approach partitions the Identity & Privilege Management environment into distinct process and technology parcels. This approach enables either a singe-step implementation or a phased migration to the new infrastructure and business processes.
Ernst & Young
Ernst & Young Security & Technology Solutions (STS) group provides independent security solutions for the world's most information-intensive organizations. STS assesses, designs, implements, and operates security solutions that enable the company's clients to achieve their business goals.
Business environments today require the ability to manage multiple versions of user identities across multiple systems and applications. For employees, customers, and business partners, the task of providing a secure environment is increasingly challenging. Ernst & Young has 400 professionals focused on security (32 hold Microsoft certifications) with experience advising Fortune 500 companies, the federal government, and the military on digital security issues.
PricewaterhouseCoopers
PricewaterhouseCoopers Security and Privacy Practice is devoted exclusively to critical information issues for Fortune 1000 organizations. The practice provides expertise in many areas, including Web security and privacy services, security integration services, information systems security and controls services, cybercrime response services, and comprehensive identity management solutions. The Security and Privacy Practice helps organizations assess, design, implement, and maintain a secure business infrastructure.
Unisys
Unisys is acknowledged worldwide as a leader in the design, development, and deployment of complex identity management solutions. This company has extensive experience with Microsoft-based solutions that incorporate Active Directory, MIIS 2003, SSO, and LDAP to provide a unified view of user, application, and network resource identity information.
The Unisys identity and access management framework incorporates biometrics, smart cards, directory services, access control, provisioning, workflow and PKI technology, and implementation services. Unisys personnel certified in Microsoft technology provide the product knowledge, IT professional consulting, design, planning, product implementation, and support services to address today's complex technology infrastructures. Unisys is a Microsoft Gold Certified Partner for Security Solutions.
Software and Hardware Vendors
Several independent software vendors (ISV) and independent hardware vendors (IHV) offer complementary products for customers implementing identity and access management solutions based on Microsoft technologies. Information provided by each vendor is provided here.
ActivIdentity
ActivIdentity is a major provider of two-factor authentication and remote access security products. In 2005, ActivIdentity acquired Protocom to provide support for Active Directory-enabled password management solutions.
ActivIdentity SecureLogin Single Sign-On enables one set of credentials to provide access to heterogeneous systems in large, distributed environments. SecureLogin also provides password management, flexible authentication, and customizable support for multiple applications and enterprise systems. SecureLogin Single Sign-On Password Management Suite enhances security, lowers administration costs, and improves employee productivity.
BMC Software
BMC Software has acquired OpenNetwork Solutions and integrated the OpenNetwork products to create the BMC Identity Management suite. The Identity Management suite covers five main solution areas: Directory Management and Visualization, Access Management, Password Management, User Administration and Provisioning, and Audit and Compliance Management.
BMC Software also provides several products that integrate with MIIS 2003, such as Business Process Manager for MIIS, and numerous third-party provisioning modules for MIIS, including SAP R/3, Sun Solaris, Oracle, and Linux. Finally, BMC Identity Management for .NET enables organizations to use their investment in Active Directory to reduce the costs of securely managing users and resources both inside and outside an organization.
Centrify
Centrify DirectControl Suite 3 extends the Microsoft Active Directory identity, access, and policy management services to UNIX, Linux, Java, and Web platforms. The suite enables organizations to integrate multiple identities quickly, without requiring intrusive changes to either Active Directory or the UNIX or Linux infrastructure. The technology enables organizations to use Active Directory to reduce administrative costs, strengthen security, and improve user productivity.
Computer Associates
Computer Associates provides a comprehensive identity and access management product line for continuously evolving computing environments, including legacy, Web, and service-oriented architectures. CA's range of identity and access management products includes eTrust Access Control, eTrust Directory, eTrust Identity and Access Management Suite and Toolkit, CA Identity Manager, eTrust Single Sign-On, eTrust SiteMinder, eTrust TransactionMinder, and eTrust Web Access Control.
DigitalPersona
DigitalPersona has worked closely with Microsoft to enable the use of fingerprint authentication for network, Web site, and application logon. By ensuring that users can be uniquely and unambiguously identified, DigitalPersona's fingerprint recognition solutions provide a natural extension of your security system, lower security administration costs, and further enhance the security features of Microsoft Active Directory and ADAM.
M-Tech Information Technology
M-Tech is a leading provider of identity management solutions. M-Tech Identity Management Suite (M-Tech IDM Suite) is a fully integrated solution for managing enterprise users and their authentication factors, including passwords, tokens, biometrics, and certificates. The suite includes M-Tech's flagship products: ID-Synch for user provisioning and P-Synch for password management. The suite also includes ID-Access for self-service resource access administration and ID-Discover to find and reconcile logon IDs across directories.
M-Tech IDM Suite runs exclusively on Microsoft Windows® 2000 Server and Windows Server™ 2003. It can provision, manage, and deactivate login accounts on every Microsoft product. M-Tech IDM Suite is integrated with MIIS 2003.
Organizations can expedite MIIS 2003 deployments using logon ID reconciliation data assembled by M-Tech IDM Suite. The suite also allows MIIS 2003 customers to implement effective password management automation, and extends the reach of MIIS 2003 to include every IT platform in the enterprise.
Passlogix
Founded in 1996, Passlogix develops software products that facilitate and secure business by managing the user names and passwords for enterprise clients. Passlogix's flagship product, v-GO Single Sign-On (SSO) can be deployed without the costs and burdens of integration usually associated with SSO solutions. v-GO SSO works with virtually any Windows, Web, Java, proprietary, and host-based application, thereby lowering IT and Helpdesk costs.
The v-GO SSO product is the first universal single sign on solution that works with all your applications without a lengthy and complex implementation and deployment process. Whether you are deploying strong authentication, implementing an enterprise-wide identity management initiative, or simply focusing on the sign on challenges of a specific group of users, the v-GO SSO product's flexible architecture supports your environment, user requirements, and financial constraints. The v-GO SSO product's patented client-side intelligence, combined with superior directory integration and a simple yet powerful administrative console, delivers the benefits of faster, more secure sign on in days — not months.
Proginet
Proginet is a leading provider of identity management, provisioning, and password management software solutions. The company's solutions address full user life-cycle management requirements, such as password management automation, self-service password reset, automated user provisioning, delegated account administration, and audit control. Proginet has a proven track record for highly secure, reliable, and scalable enterprise solutions for Fortune 2000 companies across all industry sectors, including many of the world's largest financial institutions. With a strong core competency in both distributed technology platforms and mainframe/legacy environments, Proginet's technology has achieved high levels of certification and received industry awards.
In January 2005, Proginet acquired Blockade Systems, and integrated the Blockade Systems ManageID suite into Proginet's product range. Proginet products now include SecurForce for provisioning and user life-cycle management, SecurAccess for enterprise single sign-on, SecurAccess with VASCo tokens for single sign-on with two factor authentication, and SecurPass for password management.
Quest
Quest Software acquired Vintela in July 2005. This acquisition enabled Quest to provide key infrastructure technologies to enhance the security and manageability of applications and systems for organizations with mixed environments that run Microsoft Windows, UNIX, and Linux.
Vintela Authentication Services (VAS) extends Active Directory so UNIX and Linux system administrators can centralize their authentication needs around the directory service. Because VAS integrates well with the security systems in use on Linux and UNIX, VAS automatically provides authentication to many existing Linux and UNIX services and applications. Vintela enables users to connect securely to leading J2EE application servers and Web services under the identity, authentication, authorization, and audit umbrella of Active Directory.
RSA Security
RSA Security Identity and Access Management solutions provide a compelling opportunity to gain an edge on your competitors, work more profitably with your partners and deliver a user experience that strengthens customer loyalty. Combining a successful track record in e-security, a well defined strategy, and a flexible, incremental approach to design and implementation, RSA Security allows you to address your most urgent identity management challenges today while laying the groundwork for future capabilities. RSA offers solutions for regulatory compliance, user management, single sign-on, provisioning, Web services strong authentication, access management and federated identity.
Version3
Version3 Simple Sign-On offers a uniquely robust but simple way to increase user security and productivity. Version3 Simple Sign-On transparently maintains individual application identity through Microsoft Active Directory, and therefore enhances security levels. The Version3 Simple Sign-On product's unique security architecture, ease of use, and comprehensiveness provide this product with a way to build an enterprise-wide security policy and apply it to end users. The product not only enhances security, but also dramatically improves user productivity and helps reduce Helpdesk costs